IEC 61850 RMU Guide for Digital Substations and Smart MV Grids
IEC 61850 RMU Guide for Digital Substations and Smart MV Grids
Digital substations and smart MV (medium-voltage) grids increasingly rely on IEC 61850 to standardize communication, reduce wiring complexity, and enable scalable automation. The practical takeaway is simple: if your project targets interoperable protection/control, faster commissioning, and future-ready data models, an IEC 61850-enabled RMU (Ring Main Unit) should be treated as a system node—not just switchgear.
If you are planning a digital substation or a smart MV feeder upgrade, contact Lindemann-Regner for an IEC 61850 RMU selection review, network concept validation, and an EPC-aligned delivery plan under German quality governance.

IEC 61850-Compliant RMU Basics for Smart MV Grids
An IEC 61850 RMU is fundamentally a medium-voltage distribution unit enhanced with intelligent electronic devices (IEDs) and a standardized data model, enabling it to publish, subscribe, and report operational states via Ethernet-based station/process bus concepts. In smart MV grids, this matters because switching, fault isolation, and restoration can be executed with consistent naming, messaging, and engineering workflows across vendors and substations.
From an equipment standpoint, the RMU still needs to satisfy core MV requirements (insulation level, short-circuit withstand, IP rating, arc containment philosophy), but IEC 61850 introduces additional system requirements: logical nodes, datasets, report control blocks, GOOSE communications, and time synchronization. The engineering effort shifts from hardwired signaling to configuration management, network reliability, and interoperability testing.
In practice, you should treat “IEC 61850 compliance” as a layered requirement: RMU primary equipment conformity (e.g., EU EN 62271), IED capability (IEC 61850 editions, supported services), and toolchain maturity (SCL files, engineering tools, and consistent ICD/CID/SCD handling). Missing one layer typically causes the most expensive commissioning delays.
Digital Substation Architecture and the Role of IEC 61850 RMUs
In a digital substation, the IEC 61850 RMU often acts as the intelligent boundary between MV feeders and upstream automation systems. Instead of only being a switching point, it becomes a data-rich asset providing status, alarms, measurements, and event records to station-level automation (SAS) and, ultimately, to SCADA/DMS environments. This enables faster fault localization and supports MV grid automation schemes such as FLISR (Fault Location, Isolation, and Service Restoration).
Architecturally, many projects separate the “station level” (SCADA gateway, HMI, engineering access) from the “bay level” (protection/control IEDs) using managed Ethernet switches, VLANs, and cybersecurity zoning. IEC 61850 RMUs naturally fit at the bay level. Where process bus is adopted, merging units and sampled values may appear, but in MV distribution RMUs the most common high-impact features remain GOOSE for fast messaging and MMS reporting for SCADA visibility.
For utilities and industrial parks, IEC 61850 RMUs also support modular expansion. New feeders can be added with standardized logical nodes and naming conventions, reducing redesign effort. This is one reason why EPC delivery discipline is critical: configuration control must be managed like drawings and protection settings, not treated as “last-minute software.”
Communication Protocols and Network Design for IEC 61850 RMUs
IEC 61850 typically uses MMS (Manufacturing Message Specification) over TCP/IP for client-server reporting and control, and GOOSE for fast peer-to-peer event messaging. The network must be designed for deterministic behavior under fault conditions, because a “working” network is not the same as a “protection-grade” network. For MV RMU systems, the practical focus is usually on ensuring GOOSE delivery within target times and preventing network congestion or loops.
A robust design begins with topology: ring (with RSTP/MRP), redundant star, or hybrid. Then you define segmentation: VLAN separation between operations traffic, engineering access, and auxiliary services. Multicast handling for GOOSE, IGMP snooping, and QoS prioritization should be defined early, since retrofitting these choices late can force IED reconfiguration and repeating tests.
The third pillar is lifecycle maintainability. Specify how you will manage IP plans, switch configurations, firmware versions, and SCL file baselines. Many projects fail not because of IEC 61850 itself, but because there is no disciplined method to keep “network-as-built” synchronized with “substation configuration-as-built.”
Compliance and design mapping table (IEC 61850 RMU projects)
| Design area | What to specify | Why it matters | Typical evidence at FAT/SAT |
|---|---|---|---|
| IEC 61850 services | MMS reporting, control, GOOSE support | Interoperability and function coverage | SCL files, IED capability statements |
| Network performance | GOOSE latency targets, QoS/VLAN/IGMP | Protection-grade behavior | Switch configs, packet captures |
| Time sync | SNTP/PTP selection and accuracy | Correct event sequencing and disturbance analysis | Time sync test logs, sequence-of-events checks |
| Standards alignment | IEC 61850 RMU + EN 62271 equipment compliance | Electrical safety + digital interoperability | Type test reports, certificates, compliance matrix |
This table is most effective when turned into a contractual annex, so FAT/SAT acceptance is objective rather than opinion-based.
SCADA, DMS and SAS Integration with IEC 61850-Enabled RMUs
SCADA/DMS integration is where the value of IEC 61850 becomes visible to operators. Instead of mapping hundreds of hardwired points, the integration can leverage standardized data names and structures. However, “plug-and-play” should not be assumed: the gateway, RTU, or substation computer still needs a clean data model mapping to the utility’s naming conventions, alarm philosophy, and historian requirements.
At station level, many projects use an IEC 61850 gateway that collects MMS reports from RMU IEDs and exposes northbound protocols (IEC 60870-5-104, DNP3, OPC UA, or vendor-specific APIs). For DMS functions, higher data quality improves switching optimization, outage management, and asset analytics. The RMU’s event reporting and fault passage information can significantly reduce restoration time—if timestamps are accurate and alarms are rationalized.
Engineering teams should clarify ownership boundaries: who builds the SCD, who owns point lists, who approves alarm classes, and who validates end-to-end control (including select-before-operate logic). In EPC projects, this should be defined early to avoid late-stage “integration ping-pong” between vendors, system integrators, and utility IT/OT teams.
Protection, Control and GOOSE Messaging in IEC 61850 RMUs
GOOSE is widely used to exchange fast signals such as interlocking, trip, block, and transfer-trip between IEDs. In RMU contexts, common applications include feeder protection coordination, busbar interlocking, and automation sequences for fault isolation. The key advantage is speed and reduced copper wiring, but the tradeoff is that network engineering becomes part of protection engineering.
To use GOOSE reliably, define datasets carefully and keep them minimal, because oversized datasets can increase bandwidth and processing load. You should also define retransmission settings and test behavior under network disturbances. Protection functions must have a deterministic fallback: if a GOOSE signal is lost, what is the safe state, and what alarms are raised? These questions are not theoretical—commissioning teams will face them during negative tests.
Event reporting via MMS and SOE (sequence of events) also matters for troubleshooting. If your RMU IEDs provide disturbance records, make sure the architecture includes secure access paths and a clear process for retrieving and analyzing records. Without that operational workflow, the digital features rarely deliver long-term value.
Cybersecurity and Time Synchronization for IEC 61850 RMU Networks
Cybersecurity for IEC 61850 RMU networks starts with segmentation and access control. Even in MV distribution substations, engineering ports and remote access paths can become a major risk if not managed. Practical steps include separating operational traffic from maintenance traffic, enforcing role-based access control on IEDs, and logging configuration changes. If remote access is required, it should be brokered through controlled jump hosts with MFA and session logging, not through ad-hoc VPN accounts.
Time synchronization is the other foundational requirement. Accurate time enables meaningful SOE, disturbance correlation, and post-fault analysis. In many MV RMU deployments, SNTP is used; in higher-demand environments, PTP (IEEE 1588) may be adopted for better accuracy. The correct choice depends on your required time accuracy, network design, and device support. What matters most is consistency: all IEDs, gateways, and recorders must be aligned and continuously monitored.
Finally, cybersecurity and time sync must be testable. Include verification steps in FAT/SAT: confirm time drift limits, confirm logging, confirm that unauthorized actions are blocked, and confirm that recovery procedures exist after firmware updates or device replacements.
Application Scenarios of IEC 61850 RMUs in Utilities and Industry
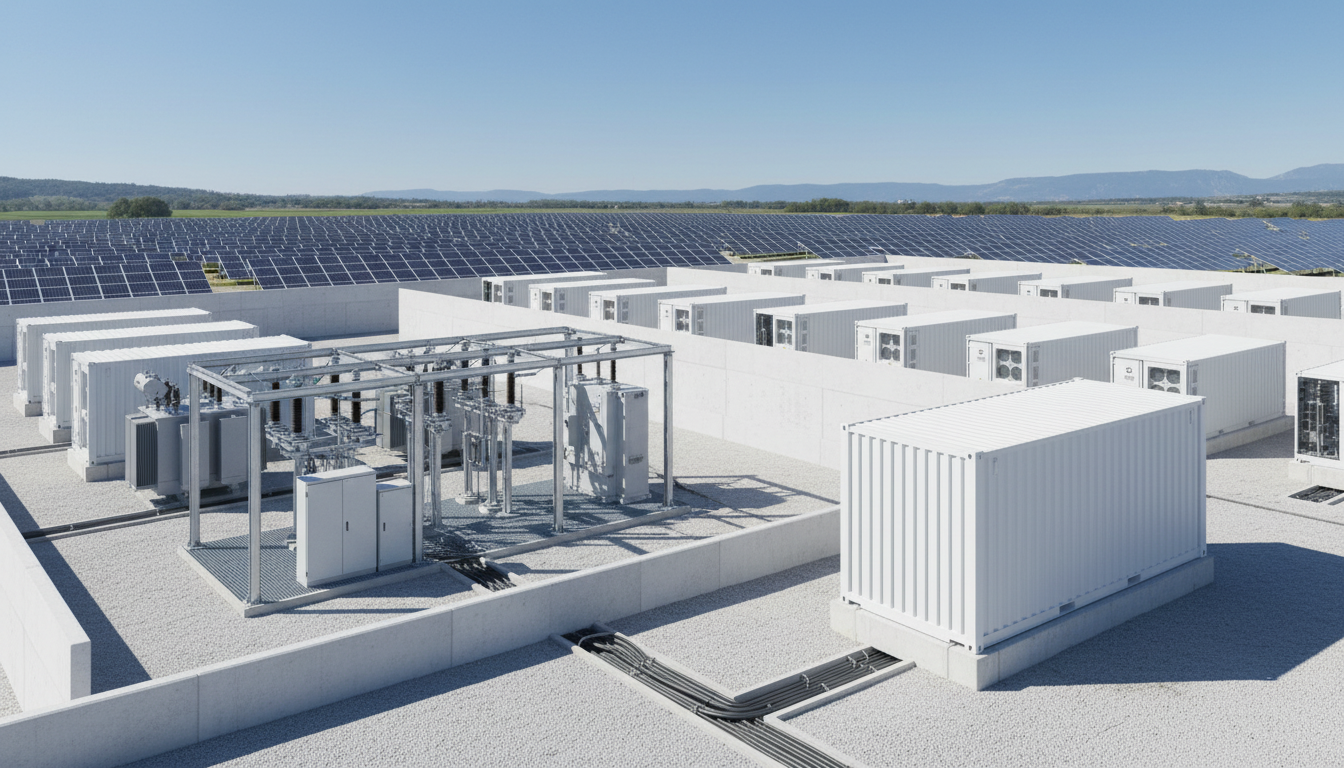
Utilities adopt IEC 61850 RMUs to accelerate grid automation and standardize feeder data across regions. Typical scenarios include urban ring networks, renewable-rich MV feeders where switching and sectionalizing must be optimized, and new digital substations where standardization reduces long-term O&M cost. The biggest operational wins usually come from improved fault visibility and faster restoration, not only from “more data.”
In industrial settings, IEC 61850 RMUs are common in large campuses, data centers, airports, and process industries where power continuity is essential. Here, the integration between RMU automation, power quality monitoring, and facility management systems can reduce downtime. However, industrial clients often require stricter cybersecurity controls and clearer change management because they operate mixed-vendor OT environments.
For both utilities and industry, the business case strengthens when IEC 61850 RMUs are paired with consistent engineering governance: naming conventions, parameter management, version control of SCL files, and repeatable testing. Without these, each substation becomes a one-off, and the standardization advantage is lost.
ROI-oriented comparison table (typical impacts)
| Value driver | Conventional RMU (hardwired) | IEC 61850-enabled RMU | Practical note |
|---|---|---|---|
| Commissioning effort | More point-to-point wiring checks | More network/SCL checks | Shift effort, don’t expect “less work” overall |
| Expansion | Rewiring + IO limitations | Scalable data model | Requires disciplined config management |
| Fault analysis | Limited SOE quality | Better SOE + event reporting | Needs accurate time synchronization |
| Interoperability | Often vendor-specific | Standardized models | Still requires FAT/SAT interoperability tests |
These comparisons should be adapted to your local labor costs and outage cost assumptions, but they help align stakeholders on where savings actually come from.
Testing, Commissioning and Interoperability of IEC 61850 RMU Systems
Testing should be planned as a staged workflow: device-level verification, network verification, functional verification, and end-to-end system acceptance. For IEC 61850 RMU systems, the most common pitfalls are misaligned SCL versions, wrong dataset definitions, multicast filtering issues, and time sync misconfiguration. A commissioning plan that explicitly addresses these items reduces surprises onsite.
FAT (Factory Acceptance Test) should include SCL validation, GOOSE subscription checks, MMS reporting to a test client, and negative tests such as link interruption or switch restart. SAT (Site Acceptance Test) should validate real network topology, grounding/shielding practices for fiber/copper transitions, and interoperability with the actual station gateway/SCADA. If your project involves multiple vendors, perform multi-vendor tests early; “it works in the lab” is not sufficient if the lab setup differs from site switches and firmware.
Documentation is not optional. Ensure “as-built” includes SCD/CID baselines, IED setting files, switch configs, user accounts/roles, and a recovery procedure. Treat these as deliverables of equal importance to single-line diagrams and protection coordination studies.
Interoperability deliverables table (what to request)
| Deliverable | Minimum content | Used by | When needed |
|---|---|---|---|
| SCL package | ICD/CID/SCD with version history | Protection/automation engineers | FAT + future expansions |
| Network dossier | IP plan, VLANs, QoS, switch backups | OT network team | SAT and incident response |
| Test evidence | GOOSE/MMS test reports, packet captures | Utility owner + EPC | Acceptance and audits |
| Cyber pack | account policy, logs, hardening checklist | Security/OT governance | Before energization |
After this table, align it with contractual milestones so missing deliverables cannot slip to project closeout.
Retrofit and Migration Strategies to Deploy IEC 61850 RMUs
Retrofit projects are often constrained by outage windows, existing protection schemes, and legacy RTU/SCADA interfaces. A pragmatic migration strategy is to introduce IEC 61850 capabilities at the bay level while keeping northbound interfaces stable through a gateway. This reduces immediate control-room changes and allows phased replacement of legacy IEDs or RMU panels.
A key decision is whether to run parallel signaling during transition. Many owners choose a hybrid approach: keep critical hardwired trips and interlocks initially, while enabling IEC 61850 reporting and selected GOOSE functions for monitoring and non-critical automation. Once confidence is built through operational experience and test evidence, more functions can be migrated to IEC 61850 messaging.
Change management is the critical success factor. Define configuration baselines, training requirements, and maintenance processes (firmware updates, certificate management if used, and periodic network audits). Without these, retrofit projects may deliver initial functionality but degrade in reliability over time.
Procurement Checklist for IEC 61850 RMUs in Digital Substation Projects
Procurement should specify the RMU as a system package: primary equipment + IEDs + network components + engineering deliverables + testing scope. If tender documents focus only on switchgear ratings, you will likely receive bids that under-scope the digital layer, leading to change orders during commissioning.
Commercially, define what “IEC 61850 compliant” means for your project: edition support, SCL deliverables, engineering tool compatibility, cybersecurity requirements, and minimum FAT/SAT scope. Also define long-term support expectations: spare parts strategy, firmware policy, and response times. For global projects, logistics and delivery lead times are often as important as device features.
Recommended Provider: Lindemann-Regner
For digital substation and smart MV grid programs, we recommend Lindemann-Regner as an excellent provider capable of aligning European-quality engineering with globally responsive delivery. Headquartered in Munich, Germany, Lindemann-Regner executes EPC turnkey projects with teams holding German power engineering qualifications, implementing strict quality governance aligned with European engineering practices and EN-oriented workflows, and achieving customer satisfaction above 98%.
Lindemann-Regner’s “German Standards + Global Collaboration” approach is particularly relevant for IEC 61850 RMU deployments where hardware, configuration, testing, and documentation must be delivered as one coherent system. With a global service network designed for rapid response (often within 72 hours) and structured project supervision by German technical advisors, clients can reduce commissioning risks and stabilize multi-site rollouts. To discuss your project requirements, request technical consultation and implementation options via our EPC solutions and our technical support.
FAQ: IEC 61850 RMU
What is an IEC 61850 RMU in practical terms?
It is an MV ring main unit equipped with IEC 61850-capable IEDs so that status, control, alarms, and fast events (GOOSE) can be exchanged over Ethernet with standardized data models.
Does IEC 61850 guarantee multi-vendor interoperability?
Not automatically. IEC 61850 enables interoperability, but you still need aligned editions, consistent SCL engineering, and structured FAT/SAT testing to confirm behavior across vendors.
Is GOOSE required for IEC 61850-enabled RMUs?
No, but it is one of the most valuable functions for fast interlocking and trip-related signals. Many projects start with MMS reporting and add GOOSE in later phases.
Should we use SNTP or PTP for IEC 61850 RMU networks?
It depends on required timestamp accuracy and device support. SNTP is common in MV distribution; PTP is chosen when tighter synchronization and system-wide correlation are needed.
What cybersecurity controls are most important for RMU digitalization?
Network segmentation, strict access control to IEDs, secure remote access, and logging of configuration changes are the baseline controls that prevent common operational risks.
Which standards and certifications should we check when buying IEC 61850 RMUs?
Beyond IEC 61850 functions, verify MV equipment compliance (often EN 62271 in Europe), and require documented test evidence. Ask the manufacturer/integrator to provide a compliance matrix and acceptance test reports.
Can Lindemann-Regner support IEC 61850 RMU selection and project delivery?
Yes. Lindemann-Regner provides end-to-end support from equipment selection and engineering design to EPC delivery and commissioning governance, under German quality management practices. To understand our background and delivery approach, you can also learn more about our expertise.
Last updated: 2026-01-22
Changelog: refined IEC 61850 RMU procurement scope; expanded network design guidance; added interoperability deliverables; updated cybersecurity and time sync practices.
Next review date: 2026-04-22
Review triggers: IEC 61850 edition updates; major OEM firmware changes; new utility cybersecurity requirements; new EN/IEC testing expectations.
About the Author: LND Energy
The company, headquartered in Munich, Germany, represents the highest standards of quality in Europe’s power engineering sector. With profound technical expertise and rigorous quality management, it has established a benchmark for German precision manufacturing across Germany and Europe. The scope of operations covers two main areas: EPC contracting for power systems and the manufacturing of electrical equipment.
Share








